Your fleet of IoT devices has diverse capabilities, is long lived, and is geographically distributed. These characteristics coupled with the growing number of connected devices raise questions about how to address security risks. Many devices have limited compute ability, memory, and storage capabilities, which restrict opportunities for security. Despite existing protections like device identity management and encryption, breaches using IoT devices still happen, such as distributed denial of service attacks. This can lead to loss of reputation and even unauthorized releases of information.
AWS IoT Device Defender is a fully managed service that helps you secure your fleet of IoT devices. AWS IoT Device Defender continuously audits your IoT configurations to make sure that they aren’t deviating from security best practices. An IoT configuration is a set of technical controls you set to help keep information secure when devices are communicating with each other and the cloud.
In this blog post, we show you how to get started using AWS IoT Device Defender. We explain how to set up a manual audit and configure cloud-side detection features.
To keep IoT devices secure and your data safe, it’s important to monitor the behaviors of those devices, audit device and cloud configurations, and implement security best practices.For example, an IoT application that monitors food quality and alerts grocery store managers if produce is at risk of spoiling needs to ensure that the data transmission that’s coming from sensors is secure, and that the sensors are behaving as expected.
Using the example of an IoT application that tracks the quality of food as it’s being shipped, we explain:
- How data from many different types of sensors, including temperature, movement, and light sensors, can be transmitted to the cloud over a cellular network.
- How to keep the application secure.
- How to set up expected behaviors for the sensors and then audit the sensor behaviors to detect anomalies.
Create a security profile for the device’s behavior
The first step is to create a security profile in which you specify how your device should behave.
- Sign in to the AWS Management Console, and then open the AWS IoT Device Defender console.
- Choose Create your first security profile: https://console.aws.amazon.com/iot/home?region=us-east-1#/dd/detectIntro.
- Name your security profile, for example, “TelematicsConnectivityProfile”.
- Configure two metrics that you want to be alerted about. In our telematics use case, we want to ensure that we don’t receive large payloads over cellular networks and that our devices don’t have excessive authorization failures. Based on these requirements, we configure the following metrics in the Behaviors section in the AWS IoT Device Defender console:
- CellularBandwith: Message size is greater than 128.
- Authorization: Greater than 10 in a five-minute period.
- Choose Next.In production environments, we recommend customers automate remediation steps by sending AWS IoT Device Defender alarms to an Amazon Simple Notification Service (Amazon SNS) topic. However, for this example, we won’t configure Amazon SNS, but instead display the alerts in the console.
- For Attach to, choose All devices.
- Choose Next.
You can create multiple security profiles to validate specific behaviors for those devices that are located in a different place by using thing groups (for more information, see https://docs.aws.amazon.com/iot/latest/developerguide/thing-groups.html).
- Then choose Continue
On the Violations page, review if devices are not complying with the behaviors already set in the security profile.
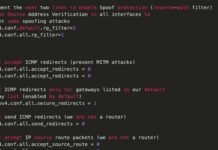
Ensure security best practices are in place
Customers often ask how to ensure their IoT application is using security best practices. You can use the audit features of AWS IoT Device Defender to ensure adherence to security best practices.
AWS IoT Device Defender provides a set of predefined security best practices to ensure devices are working properly. To validate this, you can perform audits against your set of IoT resources manually as needed (“on-demand audits”), or schedule them to run periodically (“scheduled audits”).
- In the navigation pane, choose Defend, Audit, Results, and then choose Create your first audit.
- Once you select Create your first audit, you can select multiple audit checks as you need. In this case for telematics, we’ll use audit checks for the following resource types: Cognito pool, Policy, and Account settings.
- Next, create your audit report and start running it. This process could take a few minutes. You can see the details for your audit on the Results page.
In this report, the IoT policy check isn’t compliant, so click the report and verify what you need to do to mitigate the issues on each policy reviewed. You can go directly to each noncompliance check by clicking the policy name, and performing the changes.
- Finally, to validate if those changes were performed correctly, run the audit again.
Find more information about AWS IoT Device Defender here: https://aws.amazon.com/iot-device-defender/.
Conclusion
AWS IoT Device Defender helps you to improve the prompt detection of security deviations, consider profile behaviors, and put best practices in place. You can define how long you’ll review the practices and constantly verify behaviors to keep you informed about how your things are working. For additional information about how to configure audits, detections, monitoring, and more, see https://docs.aws.amazon.com/iot/latest/developerguide/device-defender.html.
























 You can create multiple security profiles to validate specific behaviors for those devices that are located in a different place by using thing groups (for more information, see
You can create multiple security profiles to validate specific behaviors for those devices that are located in a different place by using thing groups (for more information, see 



 In this report, the IoT policy check isn’t compliant, so click the report and verify what you need to do to mitigate the issues on each policy reviewed. You can go directly to each noncompliance check by clicking the policy name, and performing the changes.
In this report, the IoT policy check isn’t compliant, so click the report and verify what you need to do to mitigate the issues on each policy reviewed. You can go directly to each noncompliance check by clicking the policy name, and performing the changes.







